According to ESET, the malicious dependency had been distributed by a recently shut down add-on repository in the Netherlands called XvBMC-NL. However, it is likely that XvBMC-NL was an unwitting participant in its distribution as it seemed to originally show up on a repo for Bubbles, later renamed Gaia.
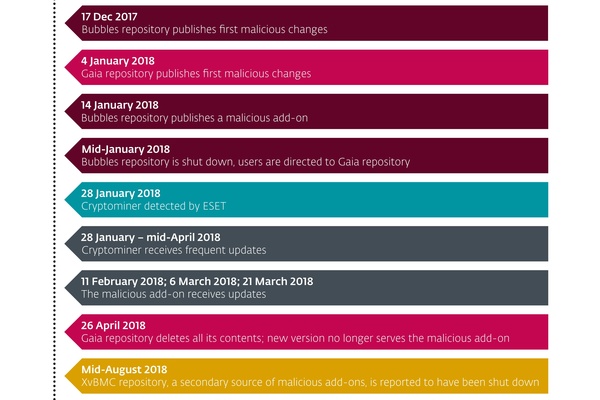
Specifically, the add-on affected is script.module.simplejson, which is a legitimate add-on that other add-ons depend on to work properly. The latest version of the add-on is v3.4.0, whereas the malicious version is v3.4.1. The malicious version reportedly showed up on the Bubbles repo back in December 2017 and was later removed from the newer Gaia report in April 2018.
The XvBMC-NL repo shut down in Holland was likely still serving the malicious version unwittingly. The problem arises when a user installed the repo and automatic updates installed the seemingly newer version, which was the malicious version.
You can easily check if you have the Add-On on your Kodi if you use the media center. In the Kodi 17 interface, open Add-Ons. Then click the Settings button (cog wheel). Open "Manage Dependencies", and then scroll down to see if SimpleJSON is installed. The version will be shown beside the add-on. If you have v3.4.1, then you have the malicious add-on and should install and run an anti-virus software to find and remove the crypto-miner it installs.
If you are on Android, you can relax as it doesn't seem to affect Android users. Regardless, you should still open the SimpleJSON add-on in the list, click update, and choose v3.4.0 if it is available from a repository to get the latest legitimate version. It should be carried by a lot of repositories.
Users of Kodi on Linux and Windows should scan their computers if they find they had the malicious add-on installed to find and remove the crypto-miner.
More information: ESET
Written by: James Delahunty @ 14 Sep 2018 15:48
