According to one security researcher, that's exactly what has to happen. Writing on his blog in the wake of the US-led operation that significantly disrupted the GOZeuS botnet yesterday, Vice President of Security Researchat Trend Micro, Rik Ferguson, argued that we should learn from this and act accordingly.
Internet Service Providers in several countries will be contacting customers who appear to be running an infected PC in order to assist them in cleaning up. Should this be considered part of ISP's long-term strategy against malware, botnets and all kinds of cybergarbage?
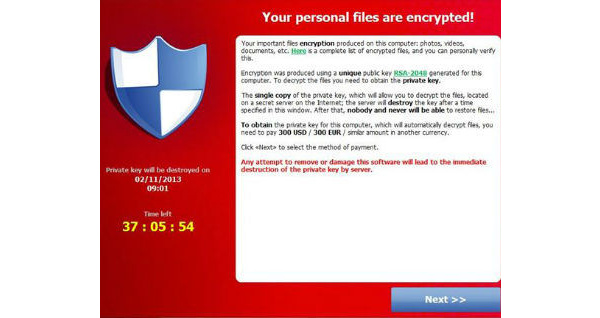
Botnets can be used to wreak havoc online. They can be used as part of distributed denial of service attacks, and of course to steal sensitive information from victims and funnel it to the gangs behind the malicious networks. They wouldn't function as well however if ISPs restricted Internet access upon detecting the threat.
"Systems that are known to be compromised should be isolated until they can be cleaned-up," Ferguson argues.
Even with all the media attention the actions taken against GOZeuS and the headlines warning about a limited window of opportunity to clean up infections now, Ferguson argues that most Internet users will forget all about it quickly.
"For the majority of internet users the story will simply pass them by," he writes. "Educational initiatives are largely only successful at preaching to the choir, so to speak "
Ferguson also goes on to raise a valid concern that news of security breaches and data losses may lead to "notification fatique", meaning people may cease to care. The solution, according to Ferguson, is to make ISPs play a much larger role in disrupting malicious threats as they attempt to propagate and act in the wild.
Ferguson's proposal: "ISPs on an on-going basis should take advantage of the threat intelligence feeds of the security industry to identify compromised systems connected to their networks. Those systems should be moved to quarantine, the account owners should be contacted and directed to resources which will enable them to clean up and rectify the situation. Until such time as the infection is remediated the computer should be able to access only limited Internet resources. Don't care will be made to care."
There's no doubt this would be an effective policy to undertake and it would be a massive blow to cybercriminals. So is Ferguson's suggestion something that needs to be pursued?
What do you think?
Sources and Recommended Reading:
It's time to quarantine infected computers: countermeasures.trendmicro.eu (by Rik Ferguson)
Written by: James Delahunty @ 3 Jun 2014 23:41
