Lenovo, who first did not take the threat seriously, was bombarded by criticism and has now released a tool to help users remove Superfish.
Says the company:
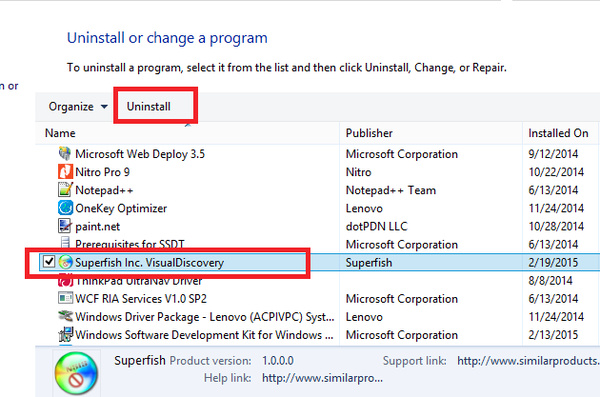
In addition to the manual removal instructions currently available online, we have released an automated tool to help users remove the software and certificate. That tool is here: http://support.lenovo.com/us/en/product_security/superfish_uninstall
We are working with McAfee and Microsoft to have the Superfish software and certificate quarantined or removed using their industry-leading tools and technologies. These actions have already started and will automatically fix the vulnerability even for users who are not currently aware of the problem.
We ordered Superfish preloads to stop and had server connections shut down in January based on user complaints about the experience. However, we did not know about this potential security vulnerability until yesterday. Now we are focused on fixing it.
Since that time we have moved as swiftly and decisively as we can based on what we now know. While this issue in no way impacts our ThinkPads; any tablets, desktops or smartphones; or any enterprise server or storage device, we recognize that all Lenovo customers need to be informed. We apologize for causing these concerns among our users for any reason � and we are learning from experience and improve what we do and how we do it. We will continue to take steps to make removal of the software and underlying vulnerable certificates in question easy for customers so they can continue to use our products with the confidence that they expect and deserve.
If you purchased a Lenovo PC between September of last year and January of this year, you are likely infected but you can check here: Filippo.io
Written by: Andre Yoskowitz @ 21 Feb 2015 0:01
